Regulatory requirements like GDPR, CCPA, and data residency have become an increasingly daunting challenge for organizations in today’s digital landscape. Compliance and regulations teams now face a massive workload to not only achieve and prove compliance but also prepare for audits and implement best practices seamlessly.
Research shows data sovereignty and compliance considerations strongly influence IT decisions and budgets by IDC. However, relying on legacy solutions leads to disparate systems that fail to work cohesively, exposing gaps and increasing costs. Outdated VPNs and identity management solutions leave organizations vulnerable.
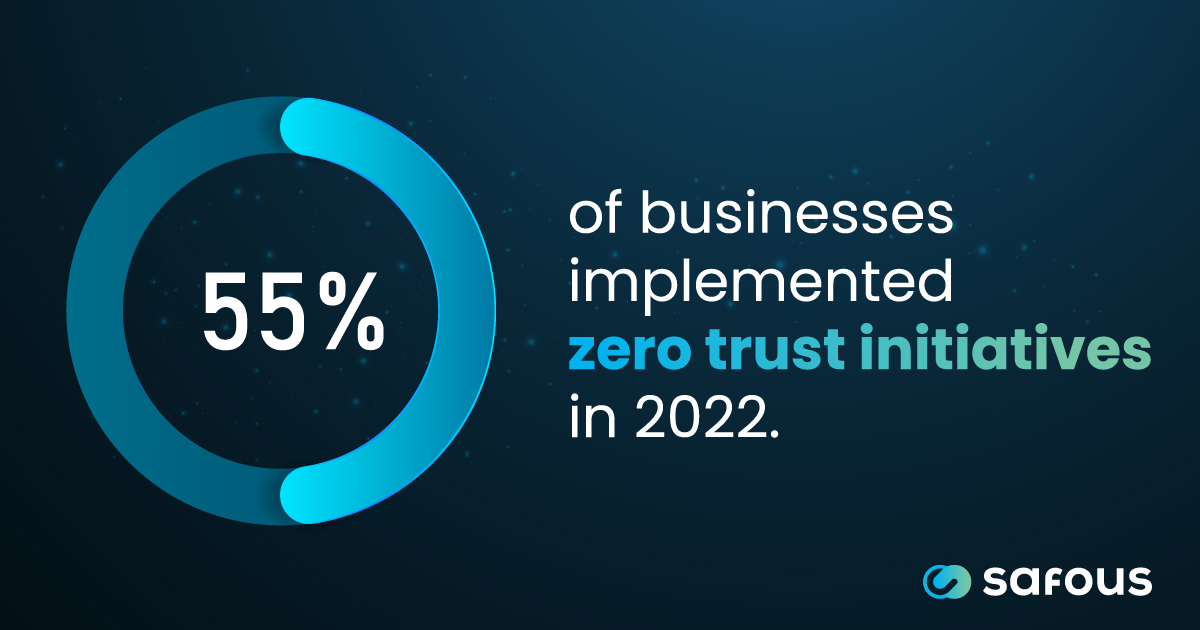
Amidst this complexity, the zero trust model has emerged as a transformative blueprint, offering a comprehensive approach to achieving regulatory compliance while fortifying security.
What Are the Limitations of Traditional Security Approaches?
Traditional perimeter security can’t keep pace in modern distributed environments. Growing adoption of remote workforces, remote access requirements, and cloud services result in businesses lacking visibility and control, leaving gaps for threats to penetrate. Sophisticated attacks increasingly bypass virtual walls via cloud misconfigurations and stolen credentials. Moreover, fragmented tools and manual monitoring overload IT teams, who are unable to track thousands of cloud endpoints.
This lack of cohesive visibility lets threats slip through the cracks, risking data breaches. Organizations need automated solutions that provide unified visibility, proactive controls, and streamlined access across on-prem and cloud workloads to strengthen security postures. By taking a data-centric approach, security can shift from reactive to proactive even as the infrastructure expands.
The Zero Trust Approach: A Holistic Solution for Compliance and Security
Zero trust is a security model that operates on the principle of “never trust, always verify.” It eliminates the concept of implicit trust, ensuring that every access request is continuously verified and authenticated, regardless of the user’s location or the device being used.
By adopting a zero-trust approach, businesses can effectively address the limitations of traditional security models and align their security posture with regulatory requirements that mandate strict access controls, monitoring of privileged actions, and robust authentication. This identity-centric approach allows organizations to holistically address compliance while evolving security to meet modern demands.
The Agentless Zero Trust Access Advantage
As perimeters dissolve, Safous’ agentless Zero Trust Access platform is a vital solution to transform security. This all-in-one platform is uniquely suited for lean IT teams and legacy systems without requiring agents or changes.
Safous layers network defenses by embracing least privilege and identity-first principles to balance access and risk. It leverages zero trust access to hide application access points, reducing attack surfaces for IT, OT, APIs, and more. Granular policies enforce context-based authorization alongside MFA and SSO to limit internal risks and secure users. Specializing in API protection, Safous applies zero trust to authenticate all connections and tailor access.
Safous reduces clutter and overhead by consolidating these diverse tools into a frictionless experience, aiding innovation for enterprises of all sizes. Its accessibility makes Safous an exemplary tool for democratizing cybersecurity across organizations of all sizes and for lean IT teams, allowing enterprises to innovate securely.
4 Pillars of Zero Trust Compliance
Effectively integrating zero trust principles into compliance strategies requires organizations to adopt a holistic approach that includes:
1. Micro-Segmentation
Micro-segmentation involves dividing the network into secure, granular zones to separate users, devices, and applications. This limits the potential impact of a breach and ensures that only authorized entities can access specific resources.
2. Least Privilege Access
Least privilege access is a principle that grants users and devices the minimum access required to perform their tasks and no more, reducing the risk of unauthorized access and minimizing the potential for data exfiltration.
3. Continuous Monitoring
By constantly monitoring user, device, application behavior, and access patterns, zero-trust platforms can detect anomalies and potential threats in real time to enable swift response and mitigation efforts.
4. Intelligent Threat Detection
By continuously monitoring user, device, application behavior, and access patterns, zero trust access can detect anomalies and potential threats in real-time. This enables swift response and mitigation through comprehensive telemetry and analytics capabilities.
By adhering to these pillars, organizations can not only reduce their attack surface and mitigate the risk of breaches but also align their security posture with regulatory requirements, ensuring data privacy and management controls are in place.
Building a Multi-Layered Defense: A Holistic Cybersecurity Stack
Achieving true cybersecurity resilience and compliance requires a multi-layered defense strategy that integrates hardware and software-based solutions. By adopting a holistic cybersecurity stack that encompasses the seven layers of the cybersecurity architecture identified in the Open Systems Interconnection (OSI) Model, your business can create a comprehensive defense posture that addresses threats at every level, from the physical hardware to the application layer.
This integrated approach not only enhances overall security but also aligns with regulatory frameworks that mandate defense-in-depth strategies and the implementation of multiple security controls to protect sensitive data and critical systems.
Safeguard Compliance With Zero Trust Access
As guardians of our organizations, we have a responsibility to protect our valuable assets and ensure compliance with regulatory standards. The zero trust blueprint offers a comprehensive approach to achieving this goal, providing a secure and controlled environment for our critical data and systems.
By embracing an agentless zero-trust approach with Safous Zero Trust Access, businesses can reduce the attack surface and mitigate the risk of breaches while simultaneously ensuring adherence to data privacy and management regulations. Furthermore, by integrating hardware and software-based solutions with this holistic cybersecurity stack, you can create a multi-layered defense that aligns with regulatory requirements and positions your organization for long-term success.
Reducing the attack surface and protecting our valuable assets are critical, but maintaining a detailed audit trail is essential in compliance efforts. Safous Zero Trust Access offers robust audit trail features without needing agent software installation, ensuring all activities are thoroughly logged and monitored. This capability is crucial for supporting compliance with the most stringent regulatory standards, providing an indispensable layer of security and accountability.
The journey towards achieving regulatory compliance begins with a mindset shift – a willingness to challenge the status quo and adopt innovative security models that can effectively counter the ever-evolving threat landscape. Contact Safous today to get started with a zero trust access solution that can help safeguard your organization’s digital future while ensuring compliance with the most stringent regulatory standards.
This blog was originally written by Roy Kikuchi for Cyber Defense Magazine on April 8, 2024. You can view the original post here.
Reference:
IDC Survey Finds Data Sovereignty and Compliance Issues Shaping IT Decisions, 2023 https://www.idc.com/getdoc.jsp?containerId=prUS50134623
How security, compliance standards prevent OSI layer vulnerabilities, 2018
Receive the latest news, events, webcasts and special offers!
Share this
You May Also Like
These Related Stories

Cyber Threats in Finance: Why Zero Trust Access Is Essential
How to Migrate to Zero Trust: The Complete Guide





